Your own ID-Server
On premise installations of SecSign ID offer the flexibility to connect with your preferred servers, services, and devices. And you can customize the SecSign ID with your own organization’s branding.
Learn Morea private key on the user’s mobile device
a PIN / password to access the private key on the smart phone.
Only if both factors are presented is the login granted. That way even if attackers gain access to one of the factors either by stealing the first or obtaining the second one, they still can’t login
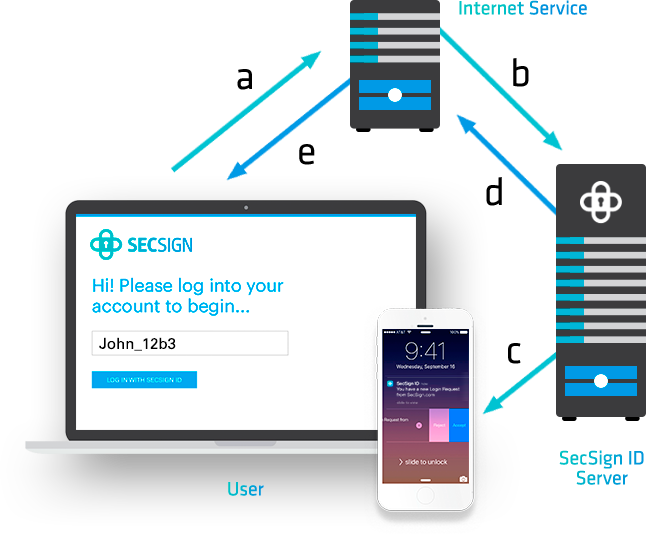
The diagram shows what the web server will request from the identity server (SecSign ID server).

The diagrams shows the messages which are exchanged between mobile device and SecSign ID server.

Authentication is simple for the user and highly secure. See for yourself with a free SecSign ID account!
The SecSign ID app allows the user to generate new key pairs for existing IDs at any time. During this process, the key on the mobile device and the key on the ID server will be replaced.
The SecSign ID session authentication is based on an RSA-encryption scheme with 2048-bit private keys. The SecSign ID app contains the private key of the user (encrypted with a PIN), and the SecSign ID server knows the users public key. During a session authentication for a login, the SecSign ID server verifies possession of the private key and knowledge of the password. The SecSign ID server evaluates the authentication request and informs the requesting service if access can be granted. If the user creates an ID on the mobile device, an asymmetric key pair (RSA) will be generated for future authentication.
The public key will be transmitted in encrypted form to the remote server and will then be deleted on the mobile device. The private key will be encrypted by a PIN and stored on the smart phone. Neither the PIN nor the private key is ever transmitted. Therefore, they cannot be intercepted by a potential attacker. This procedure protects against phishing attacks and direct attacks against the identity server.
Neither the key nor the password is ever transmitted through a network. This protects SecSign ID, your user accounts, and your critical business assets against phishing attacks, malware, or even direct attacks against the web server.
Try it now!What makes the authentication with SecSign ID so secure? It doesn’t simply secure your data, it protects it. A true Challenge Response Authentication with 2048 Bit Key Pairs makes the transfer of sensitive data completely unnecessary. We’ve been working with PKI structures for more than 18 years we know what we are doing.
The protection of the private keys on the user’s device are the main indicator how secure a challenge response authentication is. At SecSign we offer our customers the choice between the two most secure methods of key protection.

In contrast to other encryption methods, the SafeKey procedures does not provide any vulnerability to brute force attacks. The key has no detectable structure.
Even if an attacker could guess the PIN or passcode and “decrypt” the key, the attacker cannot detect whether the “decrypted” data represents the real key or not.
Only the result of the challenge-response procedure with the ID server can provide this information. The ID server, however, will lock the SecSign ID after 10 unsuccessful login attempts (or fewer attempts if you specify this on an on-premise SecSign ID server). For a brute force attack, an attacker would need many more than 10 attempts in order to successfully guess the PIN or passcode.
The SafeKey procedure is far superior than any other encryption method. It can be used for new or older, Android, iOS and Windows based devices and it is faster than any other method. And with the SafeKey procedure patented by SecSign it is way less attractive for attackers than other encryption methods used on a big scale.

The TEE is separated area in the central processing unit of the device that most newer devices have built in. It is detached from the regular processor by hardware and operates its own firmware. It only offers a few, security-relevant functions to reduce points of attack by simplifying firmware and interface as well as preventing for example direct access to the memory.
The TEE particularly protects the cryptographic keys from being copied, for example if the device is infected with malware. An asymmetric key pair is generated in the TEE and the corresponding app is granted only access to the public key. The private key is accessible solely to the TEE and information can be sent from the app to be signed by the private key via the interface. Even if the device is compromised the private key can not be simply read out.
The TEE can communicated with so-called trusted applications via the internal API. That way a secure authentication is possible without making sensitive information accessible to the rich OS.
Two-Factor Authentication is defined by having two distinct channels for communication. With the SecSign ID app you still have two encrypted channels: The browser and the app. Even if you use our SDK to integrate the 2FA into your app, the two channels remain.
So to successfully login an account secured with SecSign ID 2FA the user still needs two factors: Possession of the mobile device and either knowledge of the PIN or biometric identification.
It is not possible to intersect login attempts because the private key is located on the mobile device of the user and can’t simply be transferred to a different device.

On premise installations of SecSign ID offer the flexibility to connect with your preferred servers, services, and devices. And you can customize the SecSign ID with your own organization’s branding.
Learn More
We are happy to announce that the SecSign ID server has passed the official FIDO certification program of the FIDO Alliance. This will allow you to use the complete FIDO2/WebAuthn standard for passwordless 2FA sign-ins in your exi ...
Mehr LesenThe FIDO2 Project is a set of standards developed by the FIDO Alliance and the World Wide Web Consortium (W3C) to create a strong authentication protocol for the web. It consist mainly of the WebAuth standard for the browser part ...
Mehr LesenIn the recent weeks, home office work has increased potentially. And while employees are practicing social distancing from their home computer, attackers are working hard to exploit security issues in this situation that is unfami ...
Mehr LesenWant to learn more about SecSign’s innovative and highly secure
solutions for protecting your user accounts and sensitive data?
Use our contact form to submit your information, and a SecSign sales representative will contact you within one business day.
If you need assistance with an existing SecSign account or product
installation, please see the FAQs for more information on the most common questions. You don’t find the solution to your problem? Don’t hesitate to contact the
Product Support
I am Interested in