Your own ID-Server
On premise installations of SecSign ID offer the flexibility to connect with your preferred servers, services, and devices. And you can customize the SecSign ID with your own organization’s branding.
Learn MoreCisco ASA firewall devices offer a coordinated combination of hardware, hardened operation system and firewall software to implement an encrypted remote access to company applications and shared resources via for example SSL or IPsec. SecSign ID is integrated in the existing system and offers two-factor authentication for your VPN user.
SecSign ID is a system for real two-factor authentication (2FA) for Cisco ASA VPNs. 2FA adds another layer of security by using a second token. In this case the physical token is your smartphone.
Questions? Feel free to get in touch with us if you need help setting up your SecSign ID plugin or to request a plugin for a not yet supported environment.
GET YOUR FREE PLUGIN NOW! CONTACT USExternal access to company networks becomes more important every day. Encryption for the data transfer is important to ensure confidentiality on every level.
One factor that has to be considered is the reuse of passwords by the users for several different, sometimes even personal, purposes. Those passwords may be used to gain access to the company network and sensitive information if they have been compromised, especially if VPN connections are used. The same problem arises for passwords that are not complex enough. It is difficult for admins to push and control the use of safe passwords and the users have difficulties memorizing new and complex passwords. But the company network is only as secure as the weakest password.
These problems can be avoided by offering an additional layer of security with two-factor authentication. The login with VPN protection has to be confirmed with the smartphone in addition to providing user name and password. Attackers can not gain access by exploiting weak passwords or guessing credentials.
SecSign ID does not only protect the login but also the second factor: The smartphone. The authentication can only be confirmed if the user provides the PIN or biometric information. Specifics like IP address, service name and other information can be reviewed to monitor and limit which services the user authenticates.
By providing two security levels neither a stolen password nor a stolen smartphone allows attackers to obtain access to the network without knowing the additional PIN or providing the biometric information. In case of a lost or stolen device the user can disable the SecSign ID remotely as an additional security feature.
The distinct SecSign ID authentication works as follows:

The Cisco ASA series is a commonly used security application. It consists of an external firewall, which controls the connection between two networks. It aims in restricting the network access based on source or destination address and employed services. The data transfer is monitored and the passage of data packages is managed based on a configured set of rules. This way, unauthorized network access is prevented. The ASA box uses either IPsec or SSL to secure the VPN.
The most cost effective solution for the cooperation between two companies is the IPsec VPN. This method establishes a tunnel between both firewalls, protecting the entire route between firewall A and firewall B. A specific set of rules limits the access of either party on the essential resources and accesses.
SSL distinguishes between clientless and fat client. Clientless SSL VPN offers a secure connection to resources in the company network via SSL/TLS and web-browser. A remote access via VPN tunnel to an ASA device is created and the user does not need additional software other than the web browser.Intranet web applications, data transfer via NT/Active Directory, Email Proxies or other services are readily available with this solution.The fat client needs to be installed on the client system and offers more functionality, for example assigning static routes, implementation of virtual network cards or port rerouting.
AnyConnect Secure Mobility Client is the most widely used Cisco VPN client. It is available as desktop application for Windows, Linux and Mac as well as mobile Version for Windows Phone, Android and IOS.
The following example shows how to secure a virtual private network with the ASA box. The additional integration of the SecSign ID provides a distinctly higher degree of security by requiring the external AnyConnect Secure Mobility Client to confirm the login with his smartphone.


Is it possible for Cisco Clients like AnyConnect to display the familiar SecSign ID access pass?
Unfortunately it is not, we do not have influence on the clients to show icons or similar identification symbols. In this case, no access pass is displayed and the login on the smart phone is implemented without access pass. Instead, information about the login such as service name, IP address and other specifications are displayed after the PIN oder biometric information are provided. The user retains control on which services are authorized.
The access pass can be omitted since the Active Directory user name and corresponding password are also required, securing the login with a two step 2FA.
The network that has to be secured needs to offer an ASA or ASAv security application that makes the access via SSL- or IPSec-VPN possible. The ASA security application should communicate with a RADIUS Server to authenticate Active Directory User.
Make sure the SecSign ID is compatible with the ASA Version you use before your integrate it.
Log in to your Cisco ASDM interface and ensure the ASA firmware is version 8 or newer. That way the integration can communicate with the SecSign ID Service via Port 443.
You will need the SecSignID RADIUS Proxy for the secured communication between ASA Box and RADIUS. More information on the RADIUS Proxy can be found in the RADIUS tutorial.
The Cisco ASA security application is available as hardware and virtualised software version, ASAv. ASAv can be readily integrated in virtual environments and is provided by AmazonWebServices or can be installed at local testlabs. With an existing Cisco service agreement the virtual ASA Box can be downloaded via Cisco.
The virtualisation is based on its own OS, thus requiring a bare metal server and a hypervisor (VM Ware ESXi). Any additional Software is available as free evaluation version:
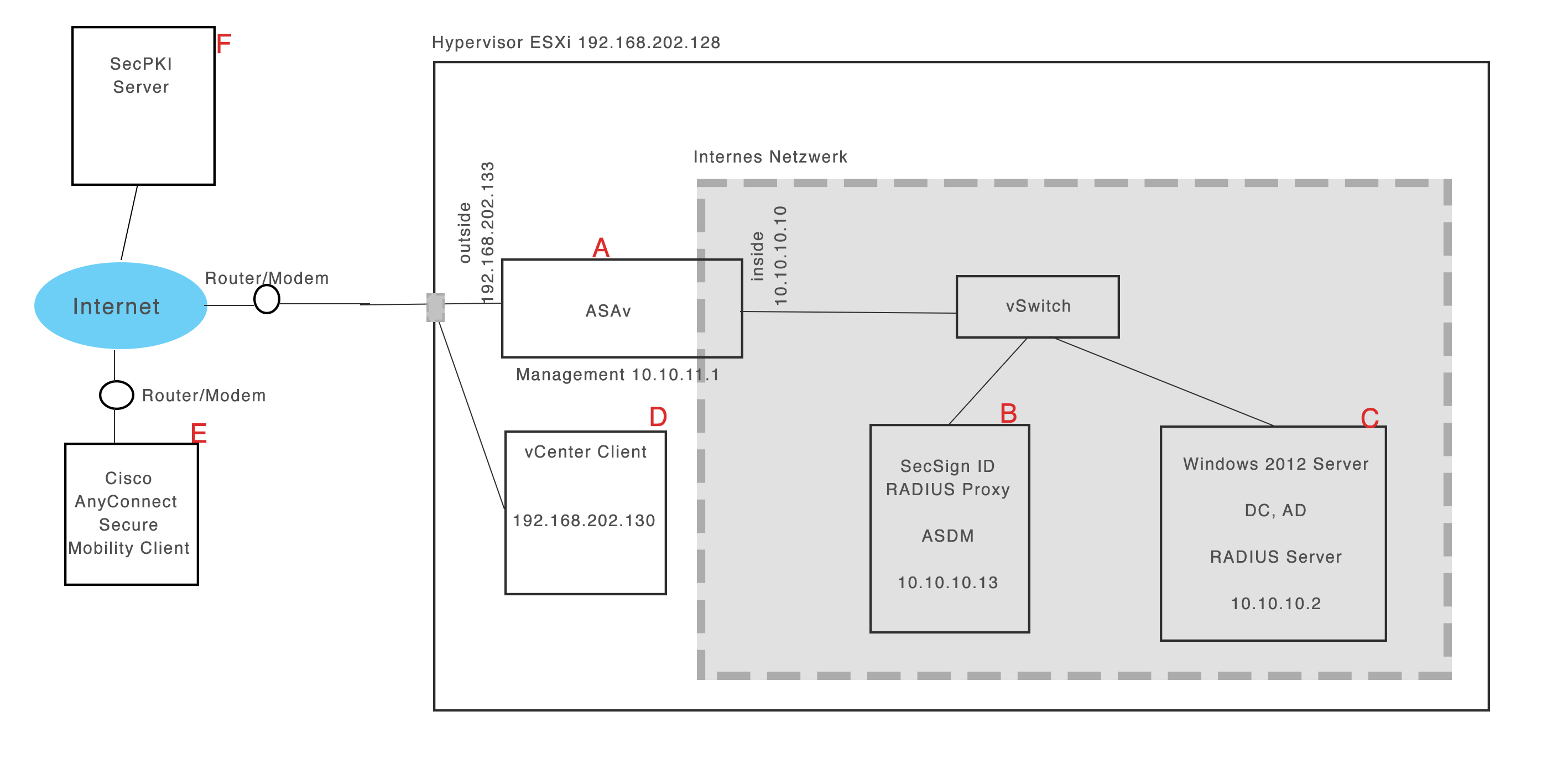
1To realise the virtualisation in a testlab the VM Ware Fusion has to be installed and VMware vSphere Hypervisor (ESXi) has to be added as virtual machine.
2System control is easier with the ESXi embedded Host Client (URL: https://ESXi-Host-IP/ui/#/login).
3Three networks or port groups respectively are generated: management, inside, outside.

4The company test server is a Windows 2012 Server (C) installed on ESXi and added to the inside network. It acts as domain controller and provides the active directory. A new test user is created.
5 Additionally, two Windows 7 or Windows Server machines (B&D) are installed on ESXi. The B machine is added to the inside net, the other one is added to the outside net. Java is installed on both.
6The vCenterClient is installed on machine D (type in the ESXi host address in the browser and follow the installation prompts).
7Now Cisco ASAv will be installed on ESXi. The vCenterClient is started on machine D to install the Cisco OVF file as virtual machine on the ESXi host. The networks are assigned to the interfaces in ASAv in the following order: 0:management, 1:inside, 2:outside. The interface IP configuration and the basic configuration is as follows:

8The ASAv Inside Interface IP can now be added to the browser on machine B. The ASDM launcher should boot and start the installation process. A SSL or IPsec VPN can be build with the ASDM Wizard. A local ASAv user is created and can then test the VPN connection from an external AnyConnect Client (E). To do so the IP address of the ASAv Box outside interface is retrieved.
9The windows server C acts as RADIUS server on port 1812 – more information on the RADIUS setup can be found in this video tutorial Cisco ASA Training 101:RADIUS.
10The ASAv Box and the RADIUS server are now acquainted to each other – more information on the ASAv Box and RADIUS setup can be found in the second video tutorial Cisco ASA Training 101:ASA&RADIUS.
One can now authenticate a user in the VPN via the external AnyConnect Client (E) with the Active Directory name.

11Yet, the login process is still based on simple passwords until the SecSign Radius Proxy is added to machine B. The proxy is a Java application and can be requested here.
More information on the RADIUS proxy setup can be found in this Tutorial. Machine B requires a connection to the SecSign Server for the two-factor authentication. In the best case this server can be operated OnPremise within the internal company network. The public server (id1.secsign.com:443) can be used as well, though one has to ensure the ASAv box does not limit the internet connection for machine B.

12The Windows Server C acts as forward RADIUS server. The RADIUS Proxy (B) is registered as RADIUS client, allowing for the ASAv box to be deleted as client. The SecSign ID (SecSign ID user name in Active Directory) is added to active directory, thus the test user (see 4.) is assigned its SecSign ID.
With the next Update for the SecSign ID RADIUS Proxy a Self Enrollment will be possible for the user. If a user is authenticated with user name and password but no SecSign ID is associated he will be able to add his ID independently.
The external AnyConnect Client can retrieve the IP of the ASAv outside interfaces when all services and servers are started (machine A, B and RADIUS proxy, C and AD, RADIUS) to start the authentication.
The AnyConnect client may cancel the VPN connection after a couple of seconds and crash when trying to reset the connection. This issue can be fixed by adjusting the MTU value of the Client OS to 1200.
The windows firewalls needs to be customized accordingly to prevent issues with the connection.
The SecSign ID RADIUS proxy requires a connection to the SecSign ID Server. If the public authentication server is used it has to be available on port 443.
The ASA Box has to forward RADIUS requests for authentication to the SecSign ID RADIUS Server and needs to be configured accordingly. It does not need to be aware of the actual RADIUS server with Active Directory connection.
To find the correspondent SecSign ID to a specific user the SecSign ID RADIUS proxy needs access to the active directory. A new user is created and the corresponding information is added to the SecSign ID RADIUS proxy configuration file.
Keywords: two-factor authentication, 2fa, SecSign ID, Cisco, ASA, VPN, ASDM, ESXi
On premise installations of SecSign ID offer the flexibility to connect with your preferred servers, services, and devices. And you can customize the SecSign ID with your own organization’s branding.
Learn More
We are happy to announce that the SecSign ID server has passed the official FIDO certification program of the FIDO Alliance. This will allow you to use the complete FIDO2/WebAuthn standard for passwordless 2FA sign-ins in your exi ...
Mehr LesenThe FIDO2 Project is a set of standards developed by the FIDO Alliance and the World Wide Web Consortium (W3C) to create a strong authentication protocol for the web. It consist mainly of the WebAuth standard for the browser part ...
Mehr LesenIn the recent weeks, home office work has increased potentially. And while employees are practicing social distancing from their home computer, attackers are working hard to exploit security issues in this situation that is unfami ...
Mehr LesenWant to learn more about SecSign’s innovative and highly secure
solutions for protecting your user accounts and sensitive data?
Use our contact form to submit your information, and a SecSign sales representative will contact you within one business day.
If you need assistance with an existing SecSign account or product
installation, please see the FAQs for more information on the most common questions. You don’t find the solution to your problem? Don’t hesitate to contact the
Product Support
I am Interested in