Your own ID-Server
On premise installations of SecSign ID offer the flexibility to connect with your preferred servers, services, and devices. And you can customize the SecSign ID with your own organization’s branding.
Learn MoreOur solution covers all setups, from securing your small-scale JIRA setup in the cloud, midsized company setups for several interfaces or managing millions of users all over the world with a solution that stays on your premise. The highest protection for your company data. Total control with your own server.
We offer the one solution you want for all your requirements, coupled with the best Two-Factor Authentication on the market. Truly secure and easy to use.
Don’t bother with inconvenient solutions, you can have both superior security and strong cryptography combined with user-optimized system for your signatures. Use it for collaborations, in-house workflows and more, improve the usability of your current system and upgrade the security with one setup.
Easy implementation for maximum security. Fully customizable – from design to security settings and implementation.


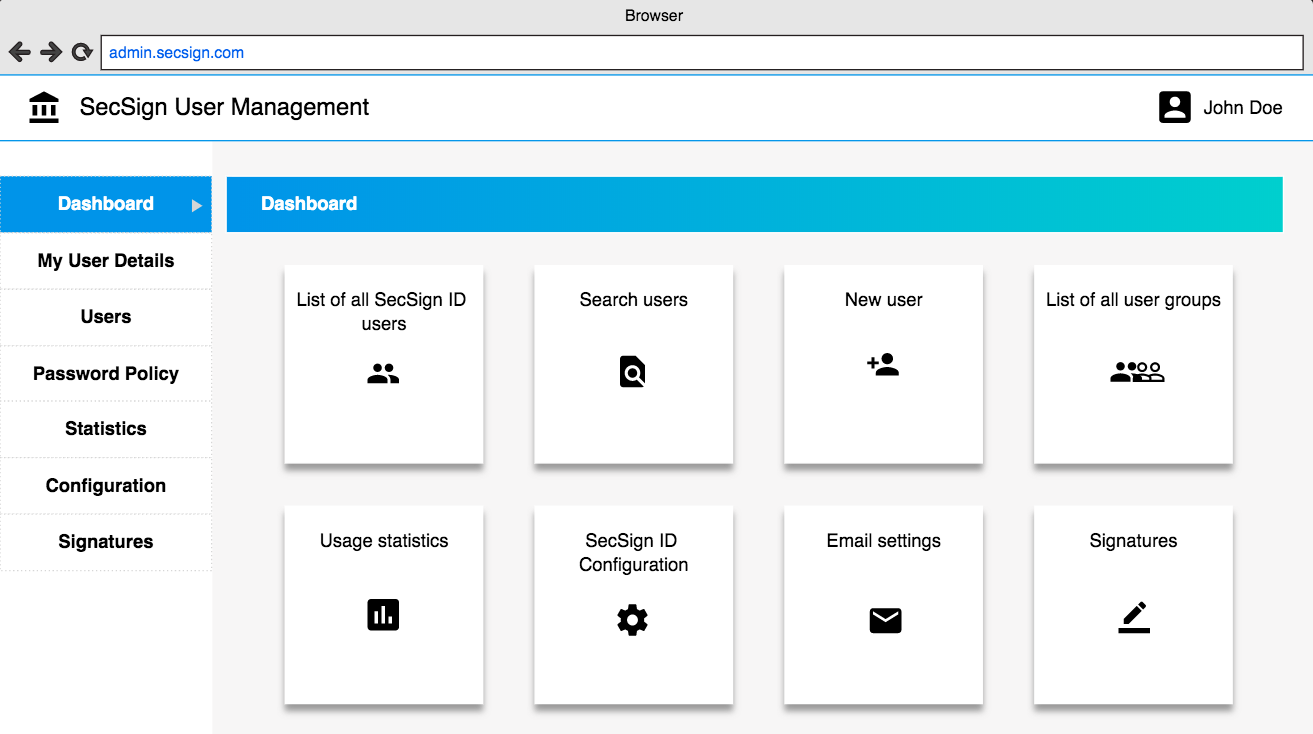
With the on-premise and managed cloud setups you can manage every detail of the user management and authentication process via the administrative panel. From comprehensive endpoint management, custom and selectively applicable rules as well as device security. Block authentication requests from outdated OS, specific locations or specific IPs. You can create different workflows for specific users, user groups, or applications in just a few simple step – manage risk profiles and resource vulnerability.
Link your user management system and manage all users and all aspects of user management and security with one IdM. More information about the SecSign ID IdM
The backend is customizable to fit your requirements, regulations and company design. You can individually define endpoint monitoring options, app and authentication options and requirements and manage your users and enrollment of new users both individually and collectively. The administrative panel user management can both be used synched to your existing user management system (for example Active Directory), or used as a single standing IdM (Identity Management) solution for all users and services.
Contact us for more information on customizations of the backend and ID app.

Your users can take care of their account without flooding the help desk with unnecessary requests. No matter if they lost their phone, need to set up a new device or want to use the ID on several devices. They can access their device list in the app and manage devices and logins. With the backup code the users can manage their account without administrative help – conveniently and secure!
The on-premise server can be integrated seamlessly into your network, no matter how complex. The following diagram gives an overview of how the server can be integrated. For more information and custom solutions, please contact us.

On premise installations of SecSign ID offer the flexibility to connect with your preferred servers, services, and devices. And you can customize the SecSign ID with your own organization’s branding.
Learn More
We are happy to announce that the SecSign ID server has passed the official FIDO certification program of the FIDO Alliance. This will allow you to use the complete FIDO2/WebAuthn standard for passwordless 2FA sign-ins in your exi ...
Mehr LesenThe FIDO2 Project is a set of standards developed by the FIDO Alliance and the World Wide Web Consortium (W3C) to create a strong authentication protocol for the web. It consist mainly of the WebAuth standard for the browser part ...
Mehr LesenIn the recent weeks, home office work has increased potentially. And while employees are practicing social distancing from their home computer, attackers are working hard to exploit security issues in this situation that is unfami ...
Mehr LesenWant to learn more about SecSign’s innovative and highly secure
solutions for protecting your user accounts and sensitive data?
Use our contact form to submit your information, and a SecSign sales representative will contact you within one business day.
If you need assistance with an existing SecSign account or product
installation, please see the FAQs for more information on the most common questions. You don’t find the solution to your problem? Don’t hesitate to contact the
Product Support
I am Interested in