
Two-Factor Authentication with Fido2 / WebAuth
01/12/2021 / 0 Comments
The FIDO2 Project is a set of standards developed by the FIDO Alliance and the World Wide Web Consortium (W3C) to create a strong authentication protocol for the web. It consist mainly of the WebAuth standard for the browser part of the authentication and the “Client to Authenticator Protocol” (CTAP) to utilize the authenticators (for example USB security sticks or smartphones).
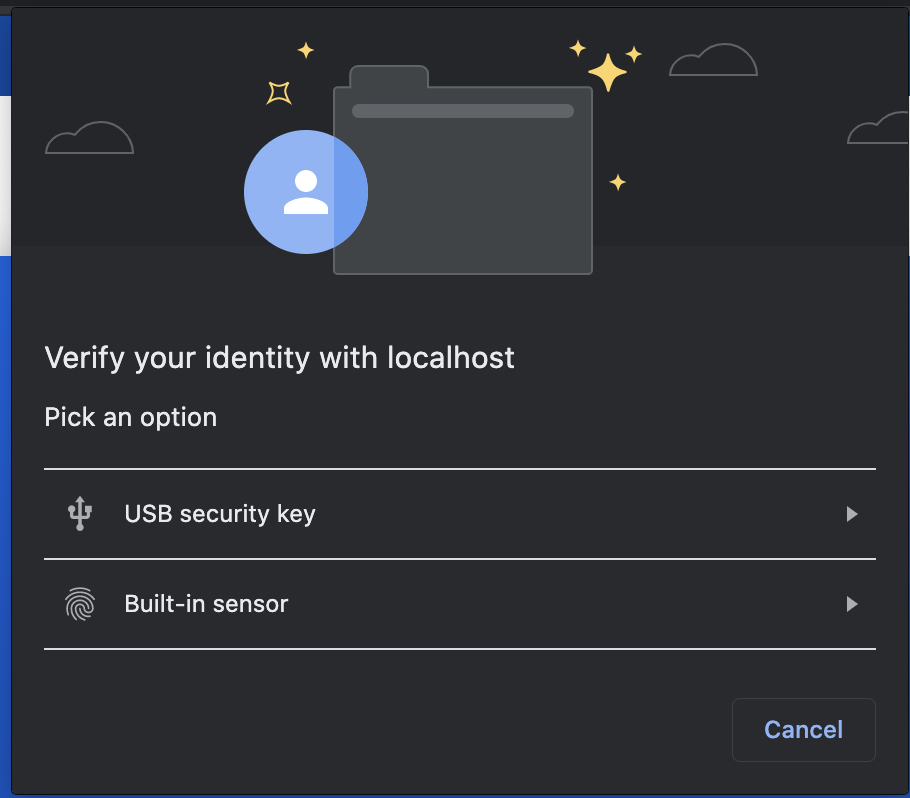
In practice the user will register one or more FIDO authenticators on a web service and can then use it to authenticate and confirm a login for example. When visiting the secured web service, the browser will ask the user to connect the FIDO authenticator to the device and press a button to register/login. Or it will utilize the build in platform authenticator by asking for a fingerprint or using the face recognition capability of the smartphone or computer. The user is then authenticated with the touch of a button.
Security Keys and Platform Authenticators
To authenticate yourself you can use many hardware FIDO authenticators like USB/BT/NFC security sticks (e.g. Yubikeys) or you can use platform authenticators that are build into the operating system of your device. The platform authenticators are available on all current mayor platforms like iOS, iPadOS, Android, Windows and macOS.
If you use a hardware authenticator you can use it on any device you need to log into a website. You just plug it in the USB port or hold it against the NFC reader of your computer or smartphone.
Platform authenticators are bound to a specific device and the operating system will manage the authentication. You can’t use these to log in on a different device. These often only work in some specific browser.
Hardware Authenticators are supported in all major browsers on all platforms. That makes them more flexibel, but you can also combine them and use more than one FIDO authenticator to authenticate a login for a web service. For example, you can use the platform authenticator in your iPhone to authenticate just with FaceID, while also having a Yubikey to authenticate when you are on your computer or use it to log in on a device which you don’t own.
All registered authenticators are bound to the hostname on which they are used. Changing the access URL will invalidate all registered authenticators for the service. In that case the user has to register the authenticator again.
Supported Platforms
Hardware authenticators are supported on all current versions of Windows, macOS, Linux, iOS, iPadOS and Android. All major browsers on these platforms support them.
Platform authenticators are also available on all current platforms, but they require a Trusted Platform Module (TPM). Most recent iPhones, iPad and Android smartphones already support this. However, it is only available on macOS Catalina (Chrome) and Big Sur with Touch ID and on Windows 10 with supported computers.
Use it with SecSign
You can use your FIDO authenticators with all our SecSign products. Our Atlassian Plugins for example support FIDO devices as an authentication method. You can use it with Confluence, Jira or Crowd as your default or as a backup method for login.

You can also use it with your own on-premise server to enable it in your custom applications and services. Use it as your primary authentication method or in combination with the SecSign ID mobile app or any other authentication method.
Backup for lost FIDO devices
If your users are using a FIDO device to authenticate to your service, you also need consider that they might loose the device. One option is to always register a second FIDO authenticator. Users can for example use a FIDO security stick like the Yubikey and also register a FIDO platform authenticator as a backup device, like their smartphone or laptop. That way they can still log in if they loose one of these.
Another option is to use the SecSign ID mobile app as a backup or alternativ authentication method.
Using the SecSign ID app as an authentication solution has other advantages as well:

- You can use it to log in on any device and are not restricted to using one (unlike a FIDO platform authenticator).
- You don’t need to have USB, Bluetooth or NFC on the device where you want to login (unlike a FIDO security stick).
- The SecSign ID is not limited to web authentication, it can also be used for all other authentication scenarios.
- The SecSign ID has an easy and secure restoration procedure if the user loses the smartphone without using a second device – just a backup code and an email address.
- And, as you authenticate on your smartphone, the device where you are performing the login can use any operation system or browser (even older ones or the smartphone the SecSign ID app run on).
If you need more information please contact us.
Categories
- Apple (11)
- Atlassian (8)
- Biometrics (6)
- FIDO (2)
- General (35)
- Secure Portal (9)
- Two-Factor Authentication (35)
- WebAuthn (1)
- Wordpress (2)
Contact Us
Sales
Want to learn more about SecSign’s innovative and highly secure
solutions for protecting your user accounts and sensitive data?
Use our contact form to submit your information, and a SecSign sales representative will contact you within one business day.
Product Support
If you need assistance with an existing SecSign account or product
installation, please see the FAQs for more information on the most common questions. You don’t find the solution to your problem? Don’t hesitate to contact the
Product Support
I am Interested in




